In the realm of cyber security, one thing is clear: the weakest link in any security system is the human being.
One can have the most state-of-the-art, bulletproof cybersecurity process in the world, but without understanding the nature of a human being, they are all are moot points once someone unauthorized gets hold of access.
In fact, a whole branch of hacking is developed around this and it’s called Social Engineering. Unlike other types of hacking, social engineering is hard to defend because human behavior is hard to predict. But a little education and awareness goes a long waya little education and awareness goes a long way, and here are four examples of social engineering attacks and tips on how to protect yourself from these types of attacks.
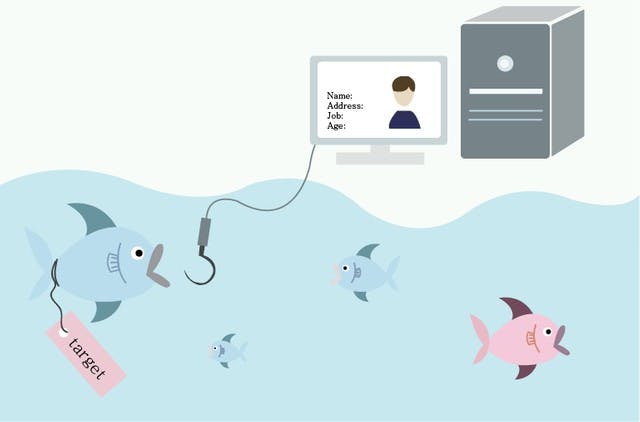
Spear Phishing
— Perhaps the most insidious phishing attack there is. Unlike regular phishing attacks, spear phishing is targeted towards a specific person based on what the attacker knows about the person, the organization they work in, and especially the work that they do.
Examples like these include someone claiming to be someone high up the organization asking the finance officer to wire money to a bank account, but in fact what they really want is for their target to give out their personal information.
To defend yourself from these kinds of attacks is to be careful with what you share online. Remember, spear phishing is crafted around you and what people know about you online, so if it’s possible to not give attackers what they want, do so.
Pretexting
— a type of social engineering attack in which someone pretends to be someone credible and trustworthy in order to gain access to privileged information, or to ask questions about someone’s personal identity.
In this type of attack, the best defense is to confirm who they say they are by doing research on the company the person claims to be from and not automatically take the person’s word for it.
Baiting
— This is done by luring people to their traps with enticing offers like free software or music, but only if they give out their personal and payment information first.
The motto for this one? Think before you click. If it’s too good to be true, it probably is.
Quid pro quo
— this literally means “something for something’. It is a type of baiting that promises a benefit in exchange for information. This benefit usually assumes the form of a service, whereas baiting frequently takes the form of a good. Attackers take advantage of what people would sacrifice in exchange for free stuff.
The most common form occurs when a hacker impersonates an IT specialist for a large company. That attackers calls a number of direct employee numbers of a specific company office and, when said hacker gets an employee on the phone, then offers the employee some kind of upgrade to their work machine. They might tell the employee to disable their anti-malware software temporarily to install a malicious ‘fix’ or software update.
In this case, it pays to know who are the IT workers in your organization, especially if it’s a large one.
EDUCATION IS KEY
Social engineering attackers prey on the human instinct to compromise their targets. It’s hard to predict how humans react, so education and awareness among users and employees remain the best shield to these kinds of attacks.
REFERENCES:
https://hackaday.com/2017/05/18/social-engineering-is-on-the-rise-protect-yourself-now/
https://us.norton.com/spear-phishing-scam-not-sport/article
https://www.bankvaultonline.com/knowledge-base/definition-of-the-day/definition-quid-pro-quo-attack/