Source code vulnerabilities are hugely critical for both dev shops and exchanges as the value stored in contract state is continually at risk of newly discovered vulnerabilities. It’s easy to start scanning your contracts today by registering on Horangi platform.
Horangi Cyber Security has completed the integration of an automated Solidity audit scanner on our Storyfier platform. Organizations can sign up and begin scanning their contracts.
How It Works
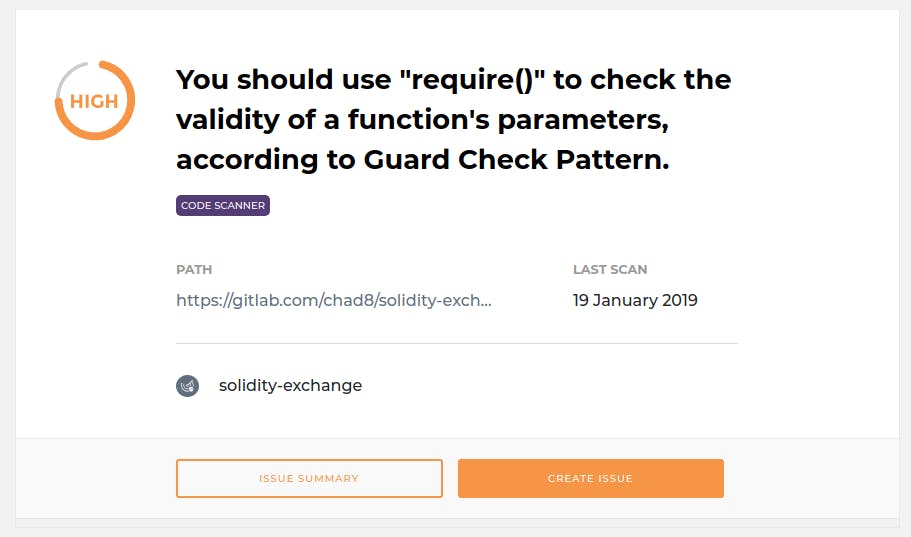
The Solidity scanner allows developers to scan their contracts for vulnerabilities. As more known vulnerability detection methods are added to the scanner, developers and executives working with Ethereum Smart Contracts will receive consistent and reliable scan results to ensure their contracts are secure.
The scanner is suitable for executives and developers who want to have consistent and regular scans of their contracts. By scheduling the scans at recurring intervals, zero-day vulnerabilities can be identified more readily. In the event that your contract has been deployed with a known security issue, the Horangi Solidity scanner can assist your team to understand the findings. Likewise, the scanner is an effective tool for developers to use during a secure software development lifecycle.
Using the scanner is easy! Sign up or log into the Horangi Storyfier platform and add a target git repo containing your Solidity code. The scanner will immediately go to work scanning the files for known vulnerabilities. The scanner will produce a findings report which is easily readable from the Storyfier dashboard.
Crypto Security & Cyber Defense
For our larger customers, such as Crypto Exchanges, Horangi offers a full stack of security products and services called our vCISO offering. We tackle two critical cybersecurity problems: there are not enough qualified cybersecurity people available to hire, and it’s difficult to communicate the business relevance of cyber security issues. Horangi is able to fill the void for companies working with cryptocurrency as regulation piles onto digital assets.
Exchanges are particularly susceptible to both Solidity code vulnerabilities and the onslaught of stringent cyber security regulation. Launching Security Tokens and trading contract tokens issued on Ethereum brings exchanges squarely into the jurisdiction of financial regulators. Horangi can help to mitigate both source code and regulatory vulnerabilities in the crypto space. Most critically, exchanges with exposure to poorly implemented dAPPs face heightened scrutiny post-incident from financial regulators after a hack occurs. More critical than regulatory pressure, is lost investor trust in your listing decisions when contracts fail to secure their investments.
Given the challenges facing the industry, working with a security partner promotes cybersecurity as a way of life for high-growth crypto platforms and builds a base-layer of defense against sophisticated adversaries. Our Solidity scanner helps to identify code issues and allows your team to monitor the security of published contracts going forward.
Horangi — Your Cybersecurity Experts
If you haven’t engaged with Horangi yet or require an Incident Response team, we have experience working with many challenging crypto security incidents and will stand by to help mitigate the damage. Before you have an incident, try out the Storyfier Solidity scanner! Not sure which cybersecurity solutions would work best for your business? Get in touchGet in touch with us today.




